Apparently, there’s been a security issue in the heart of Intel’s x86-64 kernel for over a decade, and we’re just now hearing about it. Since the kernel operates at a system level instead of an OS level, it has access to the entirety of your computer, regardless of what operating system you have installed. MacOS, Linux, Windows, and less widely known operating systems are all vulnerable to the Intel CPU kernel bug.
Unfortunately, Intel and the hardware and software vendors working on fixing this issue are forced to stay mum on what exactly the vulnerability entails. Otherwise, malicious individuals might be able to use the information to attack systems before the kernel is patched. This is a no-win scenario for the majority of computer owners because the fix for this issue has the potential to cause system slowdown because of the changes it’s making with the way the kernel interacts with your OS.
So What’s the Deal with the Intel CPU Kernel Bug?
As we stated above, the exact details of the Intel kernel vulnerability aren’t currently known. We do know that the issue centers around a memory leak that may allow malicious users to obtain data or inject code that they otherwise wouldn’t be able to. A kernel has complete control over the OS, so a security hole here is about the worst place it could be.
Am I Affected by the Intel CPU Kernel Bug?
If you have an Intel CPU, then you are affected. The full details haven’t been released yet, but it’s estimated that all Intel x86 and x86-64 CPUs manufactured in the last decade are afflicted with the bug. Newer CPUs may have less of an issue with the memory leak, but even that isn’t for sure yet.
So Who’s Going to Fix This?
While Intel will surely fix this issue in their products going forward, the security hole will need to be plugged via an OS update. Microsoft, Apple, and the various Linux distros are preparing patches that will help eliminate the vulnerability, but it will come at a cost.
How Will the Intel CPU Kernal Bug Fix Make my PC Slower?
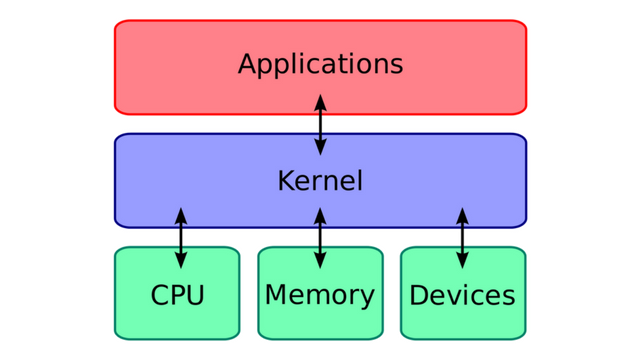
According to The Register, the bug fix will have to move the kernel’s memory from existing in all processes’ virtual address spaces to its own Kernel Page Table Isolation. This separation is necessary since user programs may be able to discern the contents of protected kernel memory. By placing the kernel memory into its own page table, applications will no longer co-exist in memory with the kernel. However, when the KPTI protocol is enabled, each time the kernel needs to be called (which is continuously) the CPU will have to switch to two separate memory addresses instead of just one.
Because of the constant switching of memory addresses, your CPU will end up dumping its cache a lot more often, which will slow down processing. In real-world terms, you won’t see a difference in some processes. Phoronix has compiled a list of benchmarks they ran using an early-build of Linux with the fix applied and some applications experienced a decline in speed of 5-to-30%.
Phoronix also tested several games, which didn’t see any significant framerate issues, but none of them ran using DirectX, which may be affected by the kernel bug fix.
What if I Have AMD?
AMD CPUs are likely not affected by the bug because of the way its architecture handles memory references. However, even though AMD has requested that the fix not be applied to its hardware, it’s possible that OS makers may scorch the earth when it comes to this bug. In that case, AMD CPUs would be affected by the kernel bug fix just the same as Intel CPUs.